Impact
Perhaps the truest measure of a scholarly institution are the footprints its faculty and students leave behind. Over the past decade, The NYU Center for Cybersecurity has defined and re-defined the boundaries of cybersecurity by addressing issues that can potentially affect the privacy, security, and safety of millions of individuals.
Below we share a few recent examples of CCS projects and programs that have continued to evolve the technology and the policies needed to face increasingly difficult attack surfaces. For more, follow our news coverage here:
- The Cybersecurity for Democracy initiative, lead by Professor of Computer Science and Engineering and CCS co-director Damon McCoy and 2021 Ph.D. graduate Laura Edelson who is now an Assistant Professor at the Khoury College of Computer Science at Northeastern University in Boston, is “a research-based, nonpartisan, and independent effort to expose online threats to our social fabric – and recommend how to counter them.” Studies conducted by the Center have exposed misinformation in political advertising and revealed the inefficiency in social media programs designed to protect children.
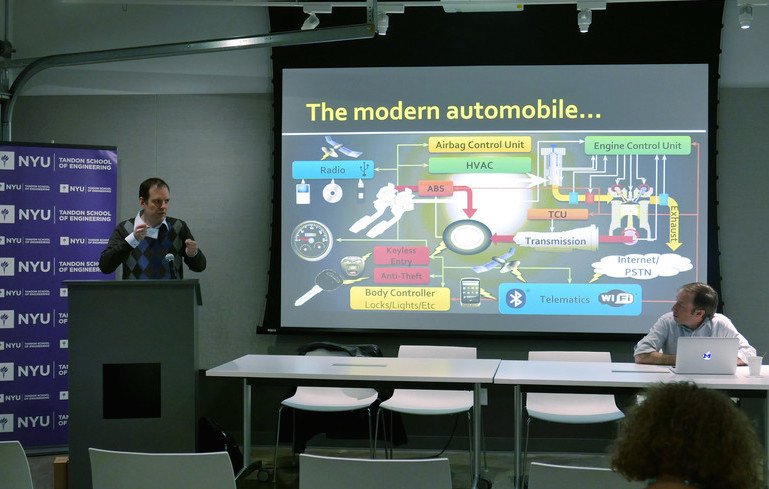
- Uptane is a framework that protects software delivered over-the-air to the computerized units of automobiles. Uptane has been adopted by several major OEMs and suppliers through its incorporation in Automotive Grade Linux. which could lead to its implementation in millions of vehicles.
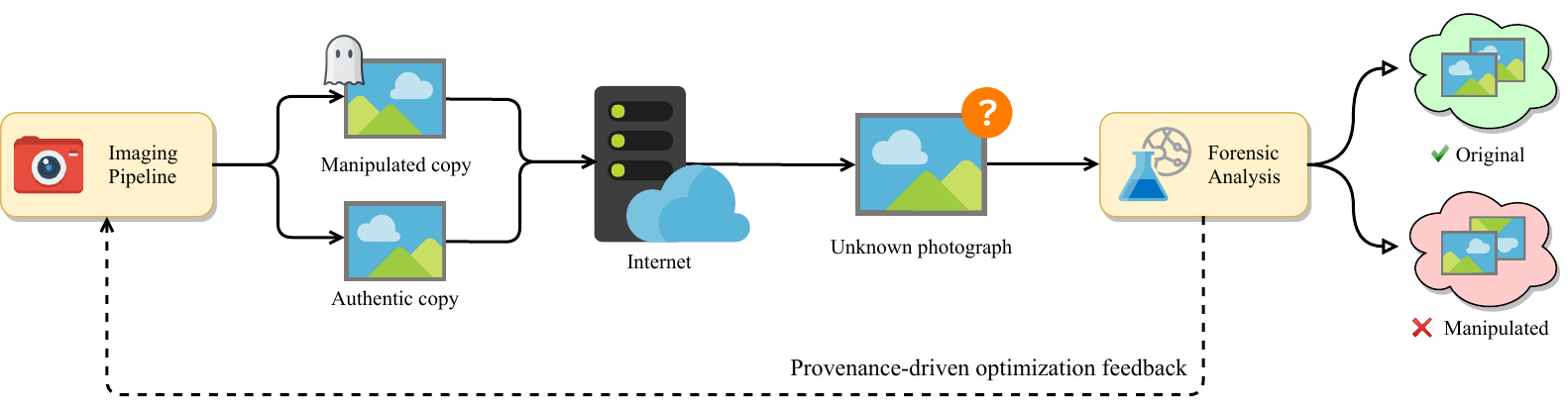
- In computer science, security has generally been piecemeal in nature, rather than a holistic operation that can guarantee the security of a project from end to end. Faculty and students at the Center for Cybersecurity have been actively engaged in changing this perspective by developing and implementing both software and hardware supply chain defenses.